Sample Ransom Note
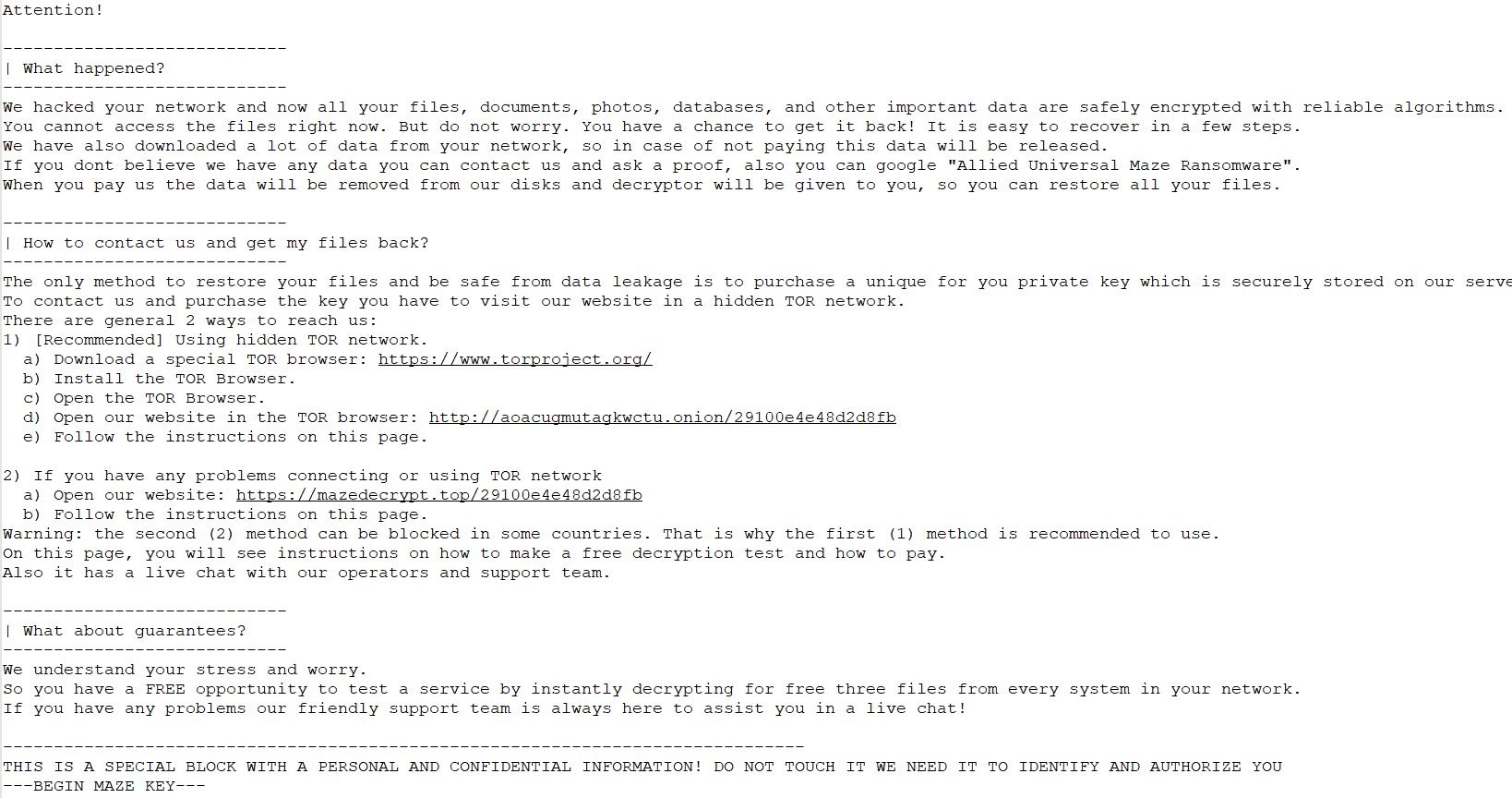
Sample Ransom Note - The two most common types of ransomware are screen lockers and. Recently, i was trying some ideas on the ransom note files of many ransomware. Implement edr solutions to disrupt threat actor memory allocation techniques. This folder contains the ransom note files of many ransomware. Web the ransomizer is a ransom note generator. The group appears to commonly deploy double extortion — of the victims that have been listed on the leak site, several of them have had some portion of their exfiltrated data exposed. Web blackbyte sample ransom note, including a warning against using the public decryptor. The fbi has observed instances where zeppelin actors executed their malware multiple times within a victim’s network, resulting in the creation of different ids or file extensions, for each instance of an attack; The three notes, despite pertaining to infections caused by three separate ransomware samples, share a similar vocabulary and carry out the first two or all three of the objectives previously mentioned. Communications with lockbit 3.0 actors;
Secure rdp ports to prevent threat actors from abusing and leveraging rdp tools. Web the ransomizer is a ransom note generator. Web sample ransom note. This results in the victim needing several unique decryption keys. Optionally, you may enter any email addresses or hyperlinks the ransomware gives you for contact (if there is no ransom note). Benign sample of an encrypted file; Web the fbi is seeking any information that can be shared, to include boundary logs showing communication to and from foreign ip addresses, a sample ransom note, communications with play ransomware actors, bitcoin wallet information, decryptor files, and/or a benign sample of an encrypted file.
Web sample ransom note. If the payment is not made, the malicious actor publishes the data on the dark web or blocks access to the. Lockbit’s active period as of june 21st, 2023, seen on its data leak site. The group appears to commonly deploy double extortion — of the victims that have been listed on the leak site, several of them have had some portion of their exfiltrated data exposed. Known for its unconventional methods and use of advanced extortion techniques, blackcat has quickly risen to prominence in the cybercrime community.
Prioritize remediating known exploited vulnerabilities. Secure rdp ports to prevent threat actors from abusing and leveraging rdp tools. Lockbit uses a dual extortion tactic, demanding that victims pay a ransom to recover their files and not release the stolen information to the public. Benign sample of an encrypted file; As this ransomware group forges its way to gain more clout, we examine its operations and discuss how organizations can shore up their defenses. Web blackbyte sample ransom note, including a warning against using the public decryptor.
If the ransom payment is made, ransomware victims receive a decryption key. Ransomware is malware that encrypts a victim’s important files in demand of a payment (ransom) to restore access. Actions to take today to mitigate phobos ransomware activity: Known for its unconventional methods and use of advanced extortion techniques, blackcat has quickly risen to prominence in the cybercrime community. Optionally, you may enter any email addresses or hyperlinks the ransomware gives you for contact (if there is no ransom note).
Benign sample of an encrypted file; The results were submitted to an academic journal to evaluate the findings. Web provided below are three examples of ransom notes: Recently, i was trying some ideas on the ransom note files of many ransomware.
I Will Share The Results Later.
This results in the victim needing several unique decryption keys. Web 16 ransomware examples. Ransomware is malware that encrypts a victim’s important files in demand of a payment (ransom) to restore access. Web this article provides many ransomware examples from 1989 to the present and discusses the most significant ransomware attacks and their variants.
Known For Its Unconventional Methods And Use Of Advanced Extortion Techniques, Blackcat Has Quickly Risen To Prominence In The Cybercrime Community.
A file which has been encrypted, and cannot be opened. Web the ransom note usually provides payment info and the threat—how to send payment and how much you need to pay, and what happens if you don't. Lockbit’s active period as of june 21st, 2023, seen on its data leak site. Benign sample of an encrypted file;
If The Payment Is Not Made, The Malicious Actor Publishes The Data On The Dark Web Or Blocks Access To The.
Communications with lockbit 3.0 actors; The group appears to commonly deploy double extortion — of the victims that have been listed on the leak site, several of them have had some portion of their exfiltrated data exposed. Web trend micro research found dozens of darkside ransomware samples in the wild and investigated how the ransomware group operates and what organizations it typically targets. The two most common types of ransomware are screen lockers and.
Implement Edr Solutions To Disrupt Threat Actor Memory Allocation Techniques.
Web sample ransom note. Those who have been hit are going to want more information, and possibly other ransomware prevention or removal solutions, like a free decrypt tool online. Web the ransomizer is a ransom note generator. Web the bitdefender ransomware recognition tool analyses the ransom note and the encrypted file samples to identify the strain of ransomware and suggest a decryption tool based on indicators.